What Is Network Monitoring and What Should It Actually Track?
Posted by Dan Schlicht
Network monitoring is the continuous process of observing a network’s health, performance, and security so teams can detect issues early, troubleshoot fast, and prove service levels. What it should actually track is anything that predicts or explains user impact: availability,…
How Often Should You Patch Your Business Systems? A Practical Schedule for Real-World IT
Posted by Dan Schlicht
Most organizations should patch critical vulnerabilities in 24 to 72 hours and apply routine updates on a predictable weekly or monthly cadence, depending on risk and business impact. If you are asking how often should you patch your business systems,…
What Is Patch Management and Why Is It Critical for Security?
Posted by Dan Schlicht
Patch management is the disciplined process of finding, prioritizing, testing, and deploying software updates that fix vulnerabilities and improve stability. It is critical for security because attackers routinely weaponize known flaws within days, and unpatched systems are among the easiest…
A Clean Start: How Simple Seasonal Prep Builds Momentum in Work and Life
Posted by Chuck Swetland
After cutting the grass for the first time this year and storing the snowblower for next winter, there’s a quiet sense of accomplishment that comes with knowing everything is handled. That’s the way I felt on Tuesday evening. The yard…
How Poor IT Documentation Increases Risk in Small Businesses
Posted by Dan Schlicht
Poor IT documentation increases risk in small businesses by creating blind spots in security, operations, and accountability. When systems fail or a cyber incident hits, missing passwords, unclear network diagrams, and undocumented vendor access slow recovery and raise the chance…
What Is IT Documentation and Why Does Your Business Need It?
Posted by Dan Schlicht
IT documentation is the written, structured record of your technology environment: how systems are built, configured, accessed, secured, supported, and recovered. Your business needs IT documentation to reduce downtime, improve security, and make daily support predictable, especially when staff change…
Why Preventative IT Maintenance Saves Money Over Time
Posted by Dan Schlicht
Preventative IT maintenance saves money over time by reducing unplanned downtime, avoiding emergency repair costs, and extending the usable life of your hardware and software. It also lowers security and compliance risk, which can otherwise create expensive incident response and…
What Is Included in a Cybersecurity Program for Small Businesses?
Posted by Dan Schlicht
A cybersecurity program for small businesses typically includes risk assessment, security policies, employee training, technical controls like endpoint protection and MFA, data backup and recovery, and an incident response plan. It also includes ongoing monitoring, vendor management, and periodic testing…
How to Identify and Prioritize IT Risks in Your Business
Posted by Dan Schlicht
To identify and prioritize IT risks in your business, start by mapping critical business processes to the systems, data, and vendors that support them, then score each risk by likelihood and impact. Focus first on risks that could stop revenue,…
What Makes a Great IT Partner vs a Basic IT Provider?
Posted by Dan Schlicht
A great IT partner does more than fix tickets and maintain devices. They align technology with your business goals, reduce risk, and take shared accountability for outcomes, not just activity. A basic IT provider may keep systems running, but rarely…
How Nonprofits Can Modernize Their IT Without Overspending
Posted by Dan Schlicht
Nonprofits can modernize nonprofit IT without overspending by prioritizing mission-critical outcomes, reducing hidden operational waste, and adopting secure cloud and managed services in phases. The key is to invest in a small set of high-impact foundations, then optimize licensing, infrastructure,…
What Are the Early Warning Signs of a Cyberattack?
Posted by Dan Schlicht
The early warning signs of a cyberattack usually show up as small but measurable changes: unusual login activity, unexpected network traffic spikes, unexplained system slowdowns, and irregular account behavior. If you spot these signals early and respond methodically, you can…
What Should Be Included in an AI Governance Policy? A Practical Checklist for Organizations
Posted by Dan Schlicht
An AI governance policy should clearly define how your organization approves, uses, monitors, and retires AI systems while meeting legal, ethical, and security expectations. It must set accountability, risk controls, data rules, and lifecycle processes that teams can follow day…
How Businesses Are Using Microsoft Copilot to Improve Productivity
Posted by Dan Schlicht
How businesses are using Microsoft Copilot to improve productivity Businesses are using Microsoft Copilot to improve productivity by drafting and summarizing content faster, turning meetings into actionable plans, and automating repetitive work inside the Microsoft 365 tools teams already use.…
What Are the Risks of Using AI Without Security Controls?
Posted by Dan Schlicht
The risks of using AI without security controls are immediate and measurable: sensitive data can leak, decisions can be manipulated, and compliance obligations can be violated. In practice, this means confidential prompts, customer records, source code, or strategy documents may…
How Manufacturers Can Reduce Cyber Risk on the Shop Floor
Posted by Dan Schlicht
Manufacturers can reduce cyber risk on the shop floor by building visibility into operational technology (OT), segmenting networks, tightening access to machines and engineering tools, and preparing for rapid recovery. The most effective programs focus on production reality: uptime, safety,…
The Masters 2026: How Augusta National Showcases the Perfect Blend of Tradition, Technology and Precision
Posted by Dan Schlicht
The Masters 2026: Tradition and technology working as one The Masters 2026 will show, once again, that Augusta National can honor golf’s most cherished rituals while operating like a modern precision laboratory. In Augusta, Georgia, the experience still feels timeless,…
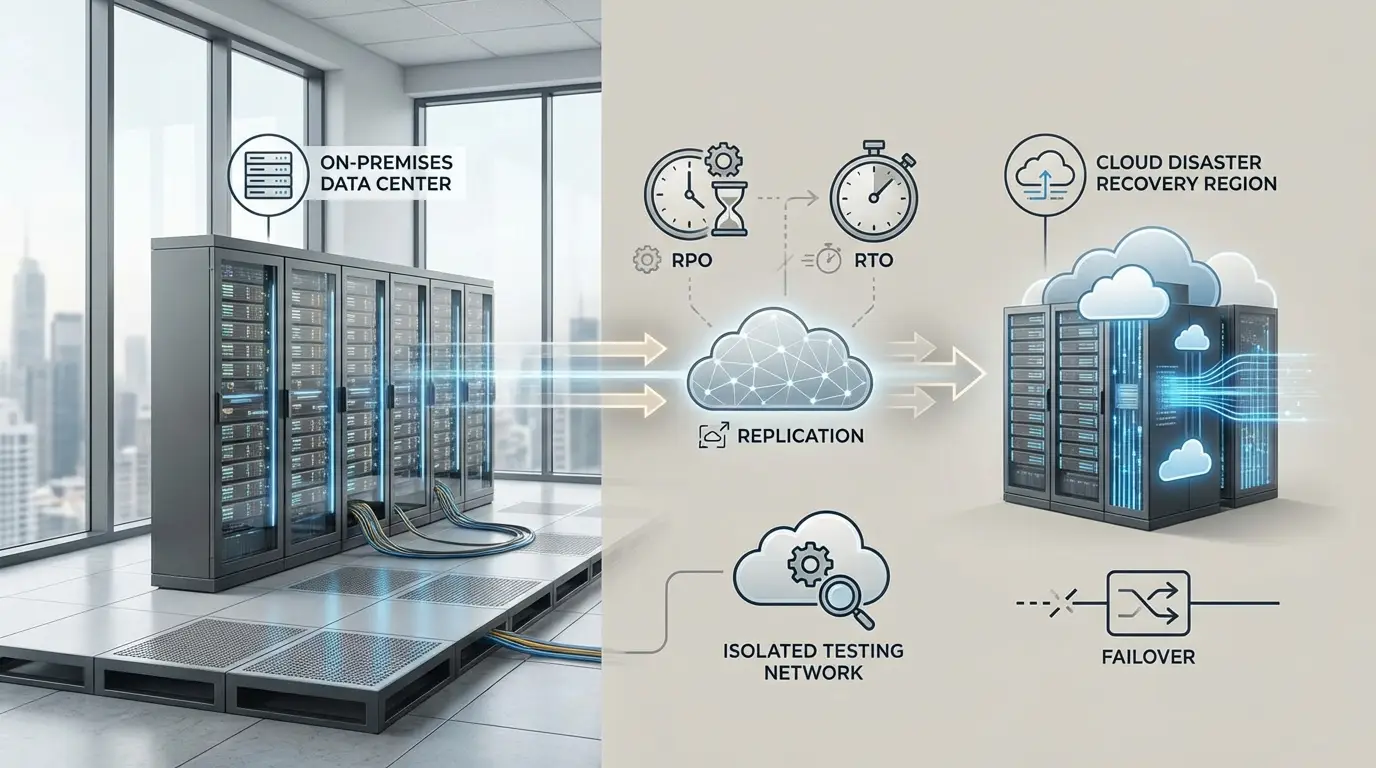
What Is Disaster Recovery as a Service and How Does It Work?
Posted by Dan Schlicht
Disaster Recovery as a Service is a cloud-based way to keep your applications and data available after an outage, cyberattack, or natural disaster by replicating systems to a provider and failing over when needed. It works by continuously copying data…
What Does a Technology Alignment Review Include? A Clear, Practical Breakdown
Posted by Dan Schlicht
A technology alignment review includes a structured assessment of your current IT environment, how well it supports business goals, and a practical roadmap to close gaps. It typically covers infrastructure, cloud, cybersecurity, applications, data, end user experience, governance, and spend,…
How to Forecast IT Costs for Growth and Expansion
Posted by Dan Schlicht
To forecast IT costs for growth, build a driver-based model that ties technology spend to measurable business inputs like headcount, revenue, transaction volume, and locations. Start by separating run costs from change costs, then quantify how each growth initiative affects…
What Are the Security Risks of Microsoft 365? A Practical Risk Map for Modern Organizations
Posted by Dan Schlicht
The security risks of Microsoft 365 mainly come from identity-based attacks, misconfiguration, data oversharing, and third-party access to your tenant. Because Microsoft 365 is cloud-first and collaboration-heavy, small gaps in settings or user behavior can lead to account takeover, data…
How to Align IT Strategy with Business Goals: A Practical Playbook
Posted by Dan Schlicht
To align IT strategy with business goals, start by translating business outcomes into measurable technology capabilities and a prioritized roadmap. Then connect funding, governance, and metrics so every major IT decision can be traced to revenue growth, cost efficiency, risk…
What Does Fully Managed IT Services Include? A Clear, Practical Breakdown
Posted by Dan Schlicht
Fully managed IT services include day to day monitoring, support, security, maintenance, and strategic planning for your technology environment under a single provider. They typically cover your endpoints, servers, network, cloud services, and user support with defined service levels and…
What Is Business Continuity Planning and Why It Matters
Posted by Dan Schlicht
Business continuity planning: what it is and why it matters Business continuity planning is the process of preparing your organization to keep critical operations running during disruptions and to restore normal operations quickly afterward. It matters because outages, cyber incidents,…