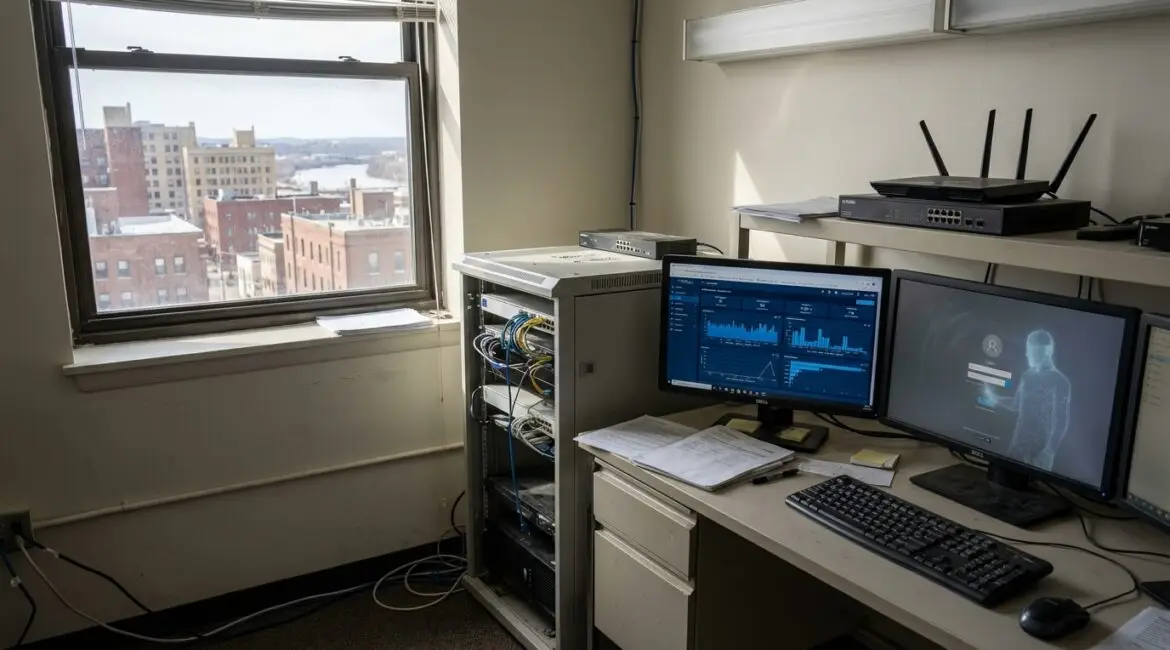
How hackers actually get into small business networks is usually not through Hollywood style “hacking,” but through everyday weaknesses like stolen passwords, phishing emails, and exposed remote access. Most compromises start with one user account or one unmanaged device, then spread through shared logins and flat networks. If you understand...