How hackers actually get into small business networks is usually not through Hollywood style “hacking,” but through everyday weaknesses like stolen passwords, phishing emails, and exposed remote access. Most compromises start with one user account or one unmanaged device, then spread through shared logins and flat networks. If you understand...
How to Choose the Right Cybersecurity Stack for a Small Business
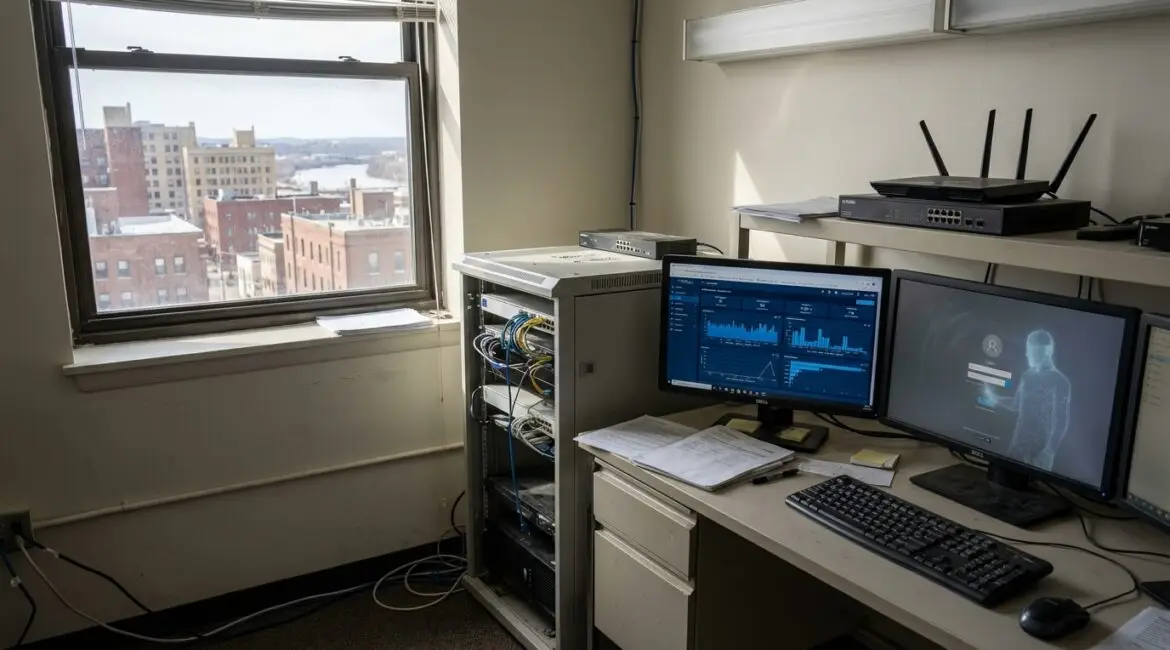
Choosing the right cybersecurity stack for a small business starts with identifying your biggest risks, your most valuable data, and the few controls that stop the most common attacks. Focus first on email and identity security, endpoint protection, and reliable backups, then layer monitoring and policies as your business grows....
How to Prevent Common Email Phishing Attempts and What Not Knowing Can Cost Your Business
To prevent common email phishing attempts, combine employee habits with technical controls like MFA, email authentication (SPF, DKIM, DMARC), and clear reporting and response procedures. Not knowing how phishing works can damage your business through wire fraud, ransomware, customer data exposure, and operational downtime. The good news is that most...