The early warning signs of a cyberattack usually show up as small but measurable changes: unusual login activity, unexpected network traffic spikes, unexplained system slowdowns, and irregular account behavior. If you spot these signals early and respond methodically, you can often contain damage before data is stolen or systems are...
What Are the Security Risks of Microsoft 365? A Practical Risk Map for Modern Organizations
The security risks of Microsoft 365 mainly come from identity-based attacks, misconfiguration, data oversharing, and third-party access to your tenant. Because Microsoft 365 is cloud-first and collaboration-heavy, small gaps in settings or user behavior can lead to account takeover, data leakage, and compliance problems in days rather than months. Why...
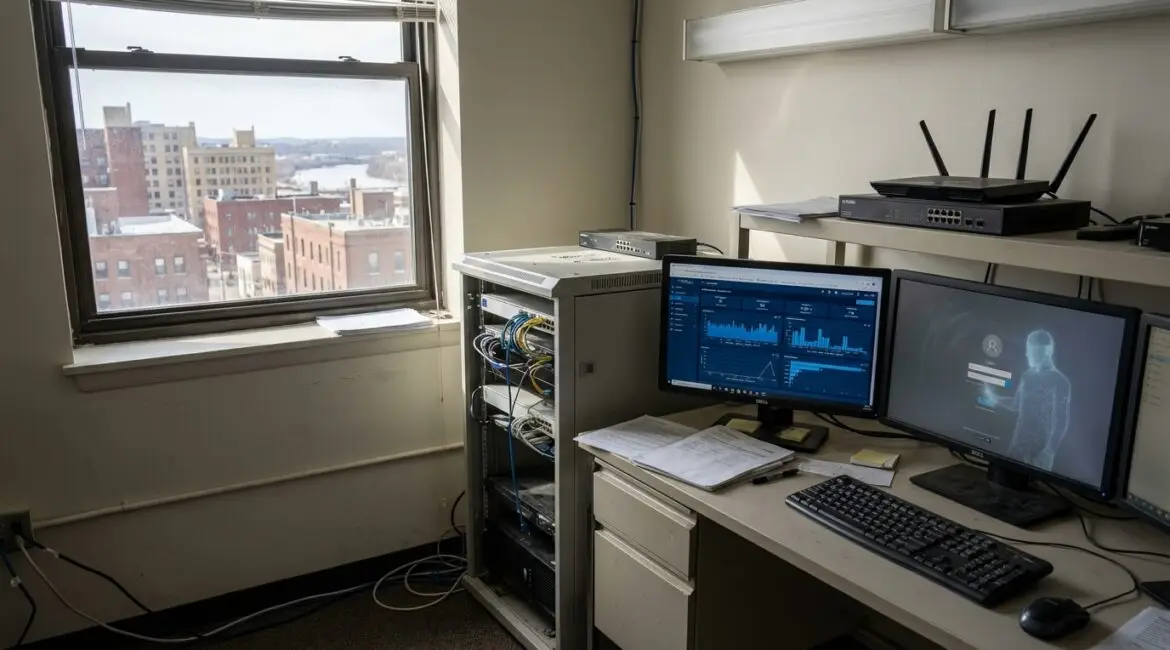
How Hackers Actually Get Into Small Business Networks
How hackers actually get into small business networks is usually not through Hollywood style “hacking,” but through everyday weaknesses like stolen passwords, phishing emails, and exposed remote access. Most compromises start with one user account or one unmanaged device, then spread through shared logins and flat networks. If you understand...