The security risks of Microsoft 365 mainly come from identity-based attacks, misconfiguration, data oversharing, and third-party access to your tenant. Because Microsoft 365 is cloud-first and collaboration-heavy, small gaps in settings or user behavior can lead to account takeover, data leakage, and compliance problems in days rather than months. Why...
How to Choose the Right Cybersecurity Stack for a Small Business
Choosing the right cybersecurity stack for a small business starts with identifying your biggest risks, your most valuable data, and the few controls that stop the most common attacks. Focus first on email and identity security, endpoint protection, and reliable backups, then layer monitoring and policies as your business grows....
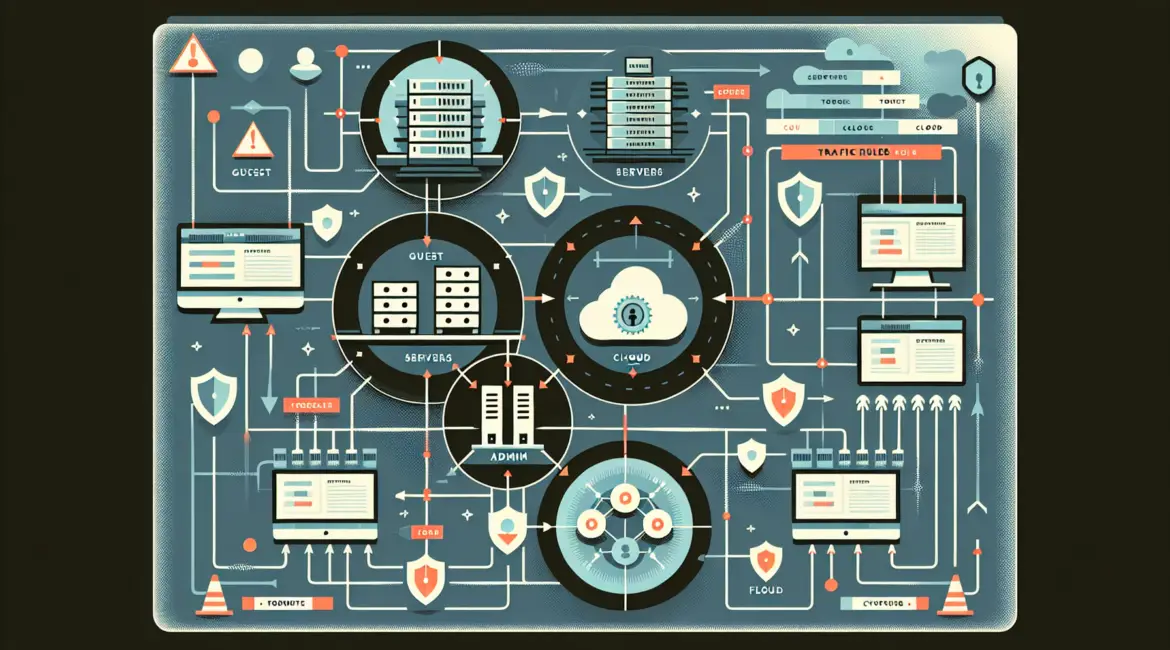
What Is Network Segmentation and Why Does It Matter?
Network segmentation is the practice of dividing a computer network into smaller, controlled zones so systems and users only access what they truly need. It matters because it limits how far cyberattacks can spread, reduces operational risk, and helps organizations meet compliance requirements. In practical terms, network segmentation turns a...