How hackers actually get into small business networks is usually not through Hollywood style “hacking,” but through everyday weaknesses like stolen passwords, phishing emails, and exposed remote access. Most compromises start with one user account or one unmanaged device, then spread through shared logins and flat networks. If you understand the real entry points, you can block the majority of attacks with targeted controls.
Why small businesses are targeted
Small businesses in places like Austin, Toronto, Manchester, and Sydney often run lean IT teams, rely heavily on cloud services, and have staff who wear multiple hats. Attackers know this and look for quick wins: outdated routers, weak passwords, and employees who approve urgent requests. Many incidents are financially motivated, including ransomware, invoice fraud, and credential theft that leads to payment card or payroll diversion.
Another driver is supply chain access. A 20 person subcontractor in New Jersey or a boutique agency in Berlin may have credentials into larger clients’ portals. Attackers may compromise the smaller firm first because the defenses are lighter, then pivot via shared tools, shared file platforms, or trusted email threads.
The most common ways attackers get initial access
Initial access is the first foothold on a device, account, or network. These are the paths that explain how hackers get into small business networks most often.
1) Phishing and business email compromise (BEC)
Email remains the number one gateway. Attackers send a convincing message that looks like Microsoft 365, Google Workspace, DocuSign, or a shipping notice. A single click can lead to a fake login page that steals credentials, or a malicious attachment that installs malware. BEC attacks are even simpler: criminals impersonate a vendor or executive and request a wire transfer, gift cards, or a change in bank details.
Small businesses are especially vulnerable when they lack DMARC, SPF, and DKIM enforcement, or when staff do not have clear verification steps for payment changes. Once an inbox is compromised, attackers often set stealthy forwarding rules and monitor conversations to time a fraudulent request.
2) Stolen passwords and credential stuffing
Many breaches start outside your company. If an employee reused a password that was exposed in a data leak, attackers can try it across popular services like Microsoft 365, QuickBooks, Slack, VPNs, and customer portals. This technique is called credential stuffing. It is automated, fast, and effective when multi-factor authentication is missing or when “legacy” logins like IMAP are still allowed.
Once attackers log in, they frequently search for file shares, HR folders, saved browser passwords, and invoices. They may also register a new MFA device if enrollment is not restricted, locking out legitimate users.
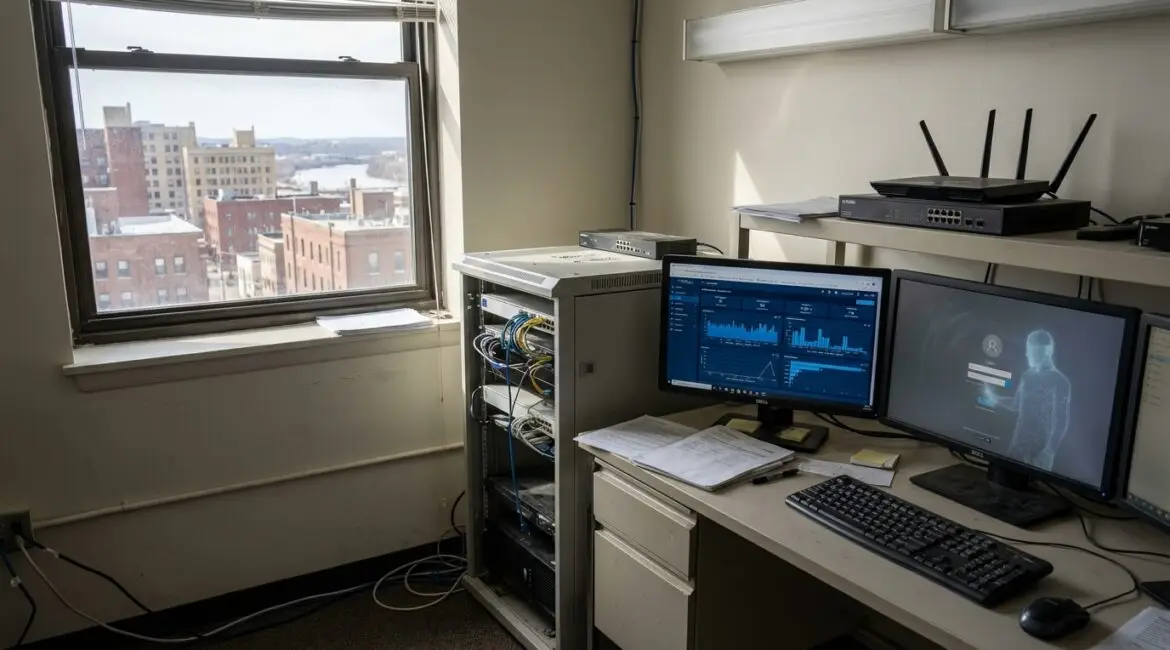
3) Exposed remote access: RDP, VPN, and remote management tools
Remote access is convenient, but it is also a common answer to how hackers get into small business networks. Open Remote Desktop Protocol (RDP) on the internet, poorly configured VPNs, and remote management tools can be discovered by scanning. Attackers try weak passwords, buy stolen credentials, or exploit unpatched vulnerabilities in edge devices.
This is frequently seen in small offices with a “set and forget” firewall, especially where the internet router provided by an ISP was never hardened. In regions with many distributed workforces, such as the US, Canada, and the UK, remote access sprawl is a regular issue as teams add tools quickly to support home and hybrid work.
4) Unpatched software and known vulnerabilities
Attackers do not need a zero day when unpatched systems are everywhere. Common targets include outdated Windows servers, old VPN appliances, unpatched WordPress plugins, and end of life network storage devices. A single vulnerable internet facing service can provide a direct path into your environment.
Once inside, attackers often use built in admin tools to avoid detection. They may create new local accounts, disable security agents, or deploy ransomware during off hours.
5) Compromised websites, forms, and third-party plugins
Small business websites often run on content management systems with multiple plugins. A vulnerable plugin or exposed admin page can allow attackers to upload web shells, redirect visitors, or steal form submissions. If your contact form emails leads directly to staff inboxes, attackers can use that channel to deliver malicious files that bypass typical filters.
This is particularly common for local businesses like dental offices, law firms, and contractors that rely on a web developer but do not have ongoing patch management or security monitoring.
6) Social engineering by phone, text, and chat
Not every breach starts with an email. Attackers call reception desks pretending to be IT support, a new vendor, or even an executive traveling. They may request a password reset, an MFA code, or remote access approval. SMS phishing and messaging app scams also drive credential theft, especially when teams use personal phones for work accounts.
In small companies, a helpful culture can be exploited if employees do not have a standard process for verifying identities and requests.
What happens after the first foothold
Understanding post compromise behavior helps you detect and contain incidents early. After gaining access, attackers typically:
- Establish persistence by creating new accounts, adding OAuth app permissions in Microsoft 365 or Google, or installing remote tools.
- Escalate privileges by harvesting passwords from browsers, probing shared drives, or exploiting misconfigurations that grant admin rights.
- Move laterally across file shares, servers, and cloud apps, especially in flat networks without segmentation.
- Exfiltrate data such as customer lists, payroll data, contracts, and financial records.
- Monetize through ransomware, invoice fraud, selling data, or using your accounts for further phishing.
In many small businesses, attackers remain undetected because logs are not centralized, alerts are not reviewed, and the first visible sign is a customer reporting a strange email or an accounting discrepancy.
Practical defenses that block the common entry points
You do not need enterprise budgets to reduce risk dramatically. The goal is to remove the easy paths that explain how hackers get into small business networks.
Harden identity and email first
- Require MFA for email, accounting platforms, remote access, and admin portals. Prefer app based or phishing resistant methods where possible.
- Disable legacy authentication and restrict MFA enrollment so attackers cannot add their own device easily.
- Deploy DMARC, SPF, and DKIM to reduce spoofing and improve inbound filtering.
- Use a password manager and enforce unique, long passwords. Monitor for leaked credentials tied to your domain.
Reduce exposed services
- Remove internet exposed RDP. Use a VPN with MFA or a secure remote access gateway.
- Patch edge devices like firewalls, VPN appliances, and NAS systems quickly, not just PCs.
- Inventory remote tools and approve a small, controlled set. Disable unused accounts immediately.
Strengthen endpoints and internal network controls
- Enable automatic updates for operating systems and key applications, with a process for exceptions.
- Use reputable endpoint protection and make sure it reports centrally so alerts are seen.
- Limit local admin rights so malware cannot easily install or spread.
- Segment critical systems like accounting, backups, and servers from everyday user devices where possible.
Make ransomware and fraud less profitable
- Implement 3-2-1 backups with at least one offline or immutable copy and test restores monthly.
- Add payment change verification for invoices and vendor bank updates using a known phone number, not email replies.
- Log and alert on email forwarding rules and unusual logins, especially from new countries or impossible travel patterns.
A simple priority checklist for small businesses
If you want a quick plan for the next 30 days, focus on:
- MFA everywhere, especially Microsoft 365 or Google Workspace and any VPN.
- Turn off legacy email authentication and enforce strong password policies with a manager.
- Eliminate exposed RDP and review firewall rules.
- Patch routers, firewalls, VPN appliances, and key servers.
- Verify backups with a real restore test.
- Train staff on phishing and payment change procedures, including phone verification.
Closing thoughts
How hackers get into small business networks is usually predictable: they exploit trust, reuse passwords, and find exposed or unpatched systems. By prioritizing identity security, reducing remote exposure, and building reliable backups and verification procedures, small businesses from Los Angeles to London can cut the most common risks quickly. Treat security as an ongoing business process, review your controls quarterly, and document who does what when something looks suspicious.
Frequently Asked Questions
What is the single most common way hackers break into small businesses?
What is the single most common way hackers break into small businesses?
Phishing and stolen credentials are the most common starting points for how hackers get into small business networks. A user clicks a link, enters a password on a fake sign-in page, and the attacker logs into email or cloud apps. Enforce MFA, disable legacy authentication, and train staff to verify links and login prompts.
Do small businesses really need MFA on every account?
Do small businesses really need MFA on every account?
Yes. MFA materially reduces how hackers get into small business networks because stolen passwords alone stop working. Start with email, VPN, remote tools, accounting, and administrator accounts. Use app-based authenticators or phishing-resistant options where possible, and restrict MFA enrollment so only approved devices can be added.
How can I tell if remote access like RDP is exposing my network?
How can I tell if remote access like RDP is exposing my network?
Check your firewall and router for inbound port forwarding, especially TCP 3389 for RDP, and review any remote management tools in use. Exposed services are a major reason how hackers get into small business networks. Remove public RDP, require VPN plus MFA, and limit access by IP and user role.
What should we patch first to reduce real-world risk?
What should we patch first to reduce real-world risk?
Prioritize internet-facing and high-privilege systems: firewalls, VPN appliances, routers, NAS devices, and email or identity platforms, then servers and endpoints. Unpatched edge devices are a common path for how hackers get into small business networks. Maintain an inventory, set patch deadlines, and verify updates actually applied.
If we get hit, what is the first action we should take?
If we get hit, what is the first action we should take?
Isolate affected devices and accounts immediately: disable suspected user logins, revoke sessions, and remove network access for infected machines. This limits how hackers get into small business networks and how far they can spread. Then preserve logs, notify your IT or incident responder, and begin recovery from tested backups.