Network segmentation is the practice of dividing a computer network into smaller, controlled zones so systems and users only access what they truly need. It matters because it limits how far cyberattacks can spread, reduces operational risk, and helps organizations meet compliance requirements. In practical terms, network segmentation turns a flat, wide open network into a set of clearly governed areas with defined rules.
Defining network segmentation in plain terms
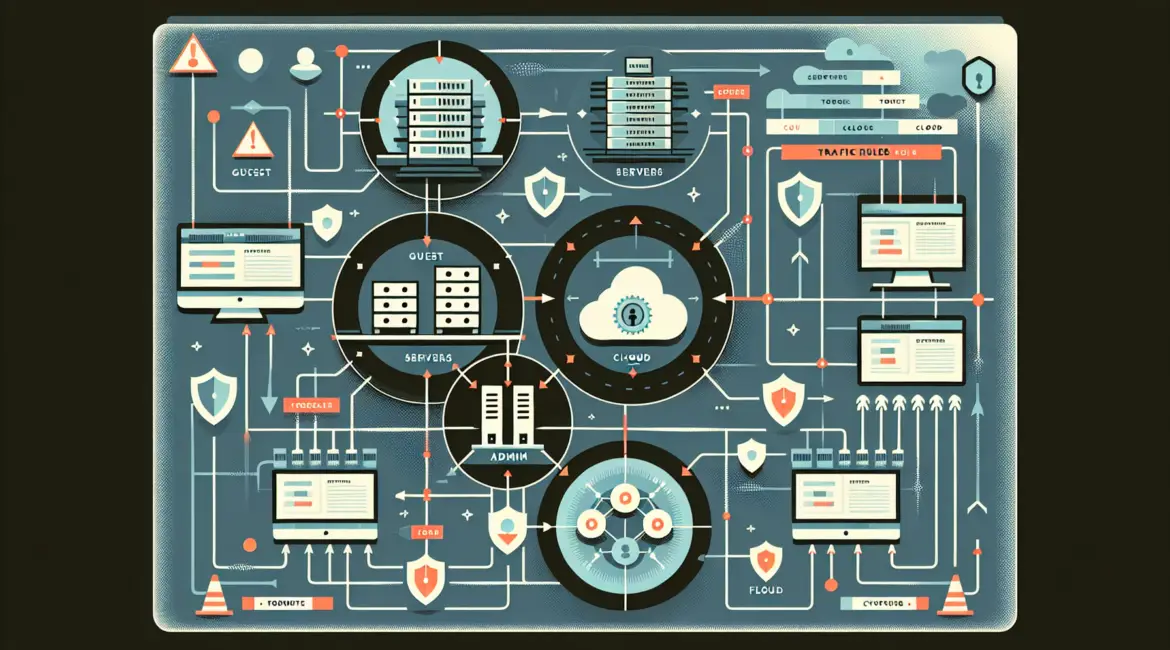
At its core, network segmentation is about controlling traffic flows. Instead of allowing every device to talk to every other device, you create boundaries between groups of assets, such as employee workstations, servers, point of sale terminals, building management systems, and internet facing services. Those boundaries are enforced with technologies such as VLANs, subnetting, firewalls, access control lists, and identity aware controls.
Segmentation can be logical, physical, or both:
- Logical segmentation uses network configuration to separate traffic, for example VLANs and routing policies.
- Physical segmentation uses separate switches, cabling, or dedicated infrastructure for high risk environments.
- Microsegmentation extends segmentation down to workload or application level, often inside data centers or cloud environments.
Why network segmentation matters: the real world impact
Many breaches become expensive because attackers move laterally after an initial foothold. A single compromised laptop can become a launch point to file shares, databases, backups, or domain controllers if the network is flat. Network segmentation breaks this chain by forcing traffic through policy checkpoints where it can be blocked, logged, and inspected.
Reducing blast radius during cyber incidents
Segmentation limits what an attacker can reach, even if they steal credentials or exploit a vulnerable device. For example, if a phishing email compromises a user in a New York office, segmentation can prevent that user network from reaching the finance systems hosted in a New Jersey data center or a cloud VPC in us east 1. This containment can be the difference between a localized cleanup and a full business shutdown.
Protecting critical systems and sensitive data
Organizations commonly have a mix of modern and legacy technology. Legacy systems, industrial control systems, and older medical devices can be difficult to patch. Network segmentation creates a protective buffer around these assets. In healthcare settings in London or Manchester, for instance, separating clinical devices from guest Wi Fi and general office networks helps prevent disruption to patient care and safeguards regulated data.
Supporting compliance and audit readiness
Security frameworks and regulations frequently expect separation of environments and restricted access to sensitive data. Payment environments handling card data, production systems, and administrative interfaces should not be broadly reachable. Network segmentation supports scoping and reduces the number of systems subject to strict controls. For multi site organizations across the EU, the US, and APAC, segmentation also helps demonstrate consistent governance and least privilege across regions.
Improving performance and troubleshooting
While security is the main driver, segmentation can also improve reliability. Separating high bandwidth traffic, such as backups or video conferencing, reduces congestion in user segments. Clear boundaries and consistent policies make troubleshooting easier, because you can quickly isolate which zone is generating errors, excessive broadcasts, or unusual traffic patterns.
Common approaches to network segmentation
There is no single best design. Effective network segmentation matches how the business operates, where data lives, and how users and applications connect. The following approaches are widely used and often combined.
VLAN and subnet based segmentation
VLANs create separate broadcast domains on the same switching infrastructure. Subnets and routing rules then control which VLANs can communicate. This is a common starting point for campuses and office networks in places like Toronto, Chicago, and Sydney because it is cost effective and aligns well with typical network hardware.
Firewall enforced zones
Firewalls, including next generation firewalls, enforce policies between zones. They can restrict traffic by IP, port, application, user identity, and device posture. A typical pattern is to place a firewall between user networks and server networks, and another between internal systems and the internet. Logging at these boundaries provides valuable incident response evidence.
Microsegmentation for data centers and cloud
Microsegmentation focuses on controlling east west traffic between workloads. In a virtualized data center or cloud environment such as AWS, Azure, or Google Cloud, you can segment by application tier, service, or sensitivity level. For example, web servers may only talk to application servers on specific ports, and application servers may only talk to databases using approved protocols. This approach is especially useful for distributed architectures spanning regions like Frankfurt, Dublin, and Virginia.
Zero trust and identity based segmentation
Modern strategies often incorporate zero trust concepts, where access decisions are based on identity, device health, and context, not just network location. This can reduce reliance on being inside the office network as a marker of trust. Identity based segmentation is helpful for hybrid workforces across cities like San Francisco, Austin, and Atlanta, where users connect from multiple networks and devices.
How to plan a practical network segmentation strategy
Network segmentation succeeds when it is intentional and maintainable. Overly complex designs can cause outages or get bypassed in the name of convenience. A pragmatic plan focuses on high value boundaries first and evolves over time.
Step 1: Inventory assets and map data flows
Start with a clear view of what you have: endpoints, servers, cloud workloads, OT devices, and third party connections. Then document how systems communicate, including ports, protocols, and authentication methods. In many organizations, this reveals surprising dependencies such as printers reaching sensitive servers or old applications using broad network access.
Step 2: Classify data and define trust zones
Create zones based on business function and sensitivity. Common examples include guest, user, developer, server, production, payment, management, and backup zones. Align zones with data classification, such as public, internal, confidential, and regulated. If you operate across multiple geographies, consider regional zones to address data residency requirements, for example separating EU hosted workloads from US hosted workloads.
Step 3: Apply least privilege rules between zones
Define explicit allow rules and deny by default where feasible. Make rules specific: source zone, destination zone, protocol, port, and identity. Avoid broad any to any exceptions. Where possible, use secure management networks for administrative access and require multifactor authentication. Each rule should have an owner and a business justification.
Step 4: Monitor, log, and validate continuously
Segmentation is not set and forget. Enable logging at inter zone controls and send logs to a SIEM or centralized logging platform. Use continuous validation, including vulnerability scanning and penetration testing, to confirm the boundaries work as intended. Review rule sets periodically to remove unused access.
Examples of segmentation that deliver quick wins
If you need immediate risk reduction, these are common starting points that work for many small and mid size organizations as well as large enterprises.
- Separate guest Wi Fi from corporate access so visitors in offices in Paris, Madrid, or Seattle cannot reach internal systems.
- Isolate servers from user workstations and require approved ports and authentication methods for access.
- Segment administrative interfaces such as hypervisors, network device management, and backup consoles into a dedicated management zone.
- Restrict east west traffic between application tiers, especially for customer facing apps.
- Create a quarantine or remediation network for devices that fail security posture checks.
Common mistakes to avoid
Network segmentation projects can stumble for predictable reasons. Avoid these pitfalls to keep security gains without harming operations.
Building zones without understanding dependencies
Blocking traffic before mapping flows often breaks applications. Always observe and document current communications, then phase in restrictions. Use temporary logging only policies to see what would be blocked before enforcing.
Too many exceptions and unmanaged rule growth
Every exception weakens segmentation. If teams request broad access, revisit application design, remote access methods, or identity controls instead of opening large network paths. Assign clear rule ownership and implement periodic rule reviews.
Relying solely on VLANs without enforcement
VLANs alone do not provide strong security if routing is permissive. Ensure there are enforcement points, such as firewalls or well managed access control lists, and ensure device configurations are protected with strong authentication and change control.
Choosing tools and technologies that fit your environment
Your best mix depends on size, complexity, and whether you are on premises, cloud first, or hybrid.
- Small organizations often start with VLANs plus a capable firewall and strong identity controls.
- Enterprises may use multiple firewall tiers, network access control, microsegmentation platforms, and centralized policy management.
- Cloud heavy teams typically lean on security groups, network policies, private endpoints, and service mesh controls.
Regardless of tooling, network segmentation should be documented, tested, and aligned with incident response plans so teams know how to contain threats quickly.
Bottom line: segmentation is a business continuity control
Network segmentation is not just a technical best practice. It is a practical way to reduce the likelihood that a single compromised device, vendor connection, or misconfiguration becomes a company wide crisis. By defining zones, enforcing least privilege, and continuously validating controls, organizations can improve resilience, meet compliance expectations, and keep critical services available. If you approach segmentation as an evolving program with clear ownership and measurable outcomes, it becomes a durable part of operational risk management.
Implementing network segmentation is most successful when security, IT operations, and business stakeholders collaborate on priorities, testing, and change management. A phased rollout, strong documentation, and continuous monitoring help ensure the result is both secure and practical. For organizations operating across multiple sites and regions, this disciplined approach supports consistent protection and reliable growth.
Frequently Asked Questions
What is the difference between network segmentation and microsegmentation?
What is the difference between network segmentation and microsegmentation?
Network segmentation typically separates broad zones such as users, servers, and guest networks using VLANs, subnets, and firewalls. Microsegmentation applies finer controls between individual workloads or application tiers, often in virtualized or cloud environments. Many organizations use both, starting with network segmentation and adding microsegmentation for high value systems.
Does network segmentation slow down a network?
Does network segmentation slow down a network?
Network segmentation can improve performance by reducing unnecessary broadcasts and isolating heavy traffic like backups. Poorly designed rules or undersized firewalls can add latency, so capacity planning matters. Use monitoring to validate throughput and adjust policies. Well implemented network segmentation usually delivers better stability with minimal user impact.
How do I know where to start with network segmentation in a small business?
How do I know where to start with network segmentation in a small business?
Start network segmentation with the highest risk boundaries: separate guest Wi Fi from corporate access, isolate servers from user PCs, and place administrative interfaces on a dedicated management network. Then restrict access to only required ports and services. Document rules and test changes after hours to avoid disrupting daily operations.
Is network segmentation required for compliance standards like PCI DSS or HIPAA?
Is network segmentation required for compliance standards like PCI DSS or HIPAA?
Many standards strongly encourage or effectively require network segmentation to reduce scope and protect sensitive systems. PCI DSS uses segmentation to limit the cardholder data environment, and HIPAA aligned programs use it to safeguard systems handling regulated health data. Network segmentation also helps produce clearer audit evidence through enforced boundaries and logs.
What tools are commonly used to implement network segmentation?
What tools are commonly used to implement network segmentation?
Common tools for network segmentation include managed switches for VLANs, routers for inter VLAN routing, firewalls for policy enforcement, and network access control for device based restrictions. In cloud environments, security groups and network policies are key. Centralized logging and a SIEM help validate that network segmentation rules work as intended.